Guten Tag!
Our new German office is now open,
supporting all of our German based customers.
We are
PASSIONATE
Our passion for product and for our customers brands is what sets us apart.
How can we help?
Promotional Merchandise Packs
delivered in custom packaging.
Wellness Journals
Help employees manage their daily activities and improve their physical and mental wellbeing.
Guten Tag!
Our new German office is now open,
supporting all of our German based customers.
We are
PASSIONATE
Our passion for product and for our customers brands is what sets us apart.
How can we help?
We are
RESPONSIBLE
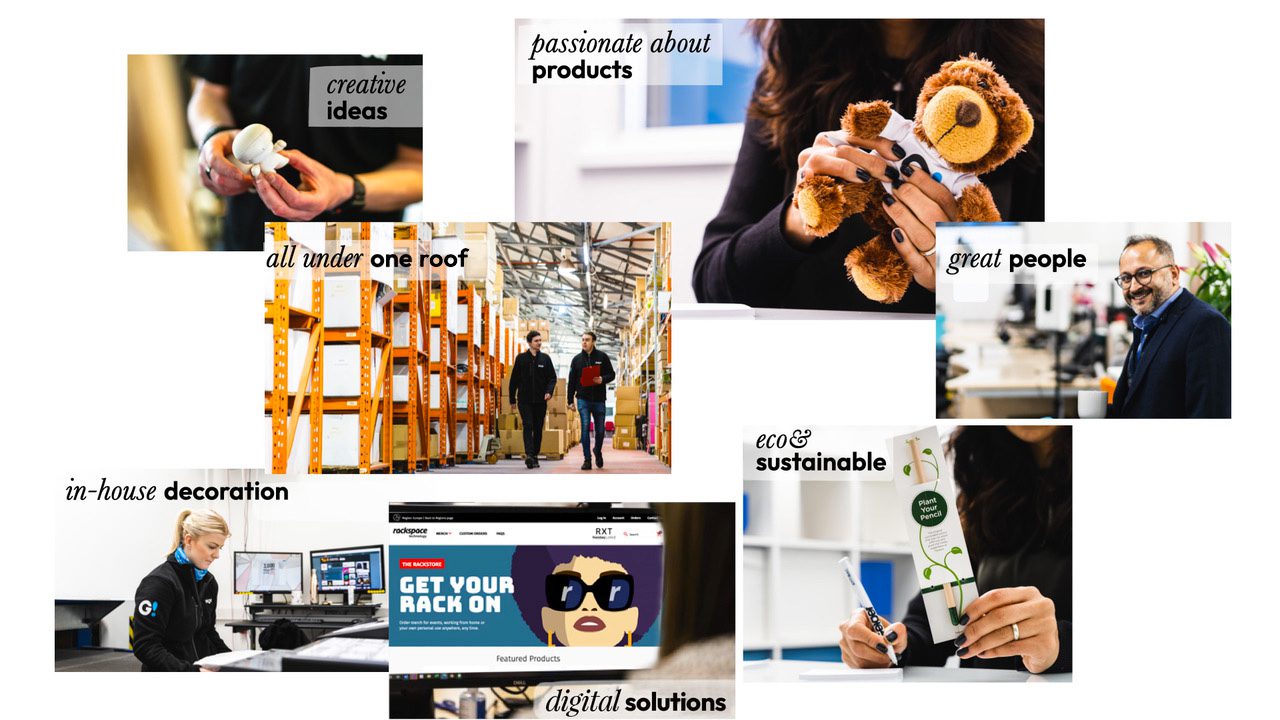
We are the promotional Merchandise Specialists.
Creative ideas, innovative products, digital solutions, in-house decoration,
warehousing, fulfilment & sustainable best practices all in one place!
With creativity central to our success and longevity, our teams are now embracing the need to promote more sustainable product initiatives to supply our clients with ideas that they can rely on to engage customers and promote their brand positively.
As a partner to your brand, and the planet, we have the skills and experience to deliver exceptional merchandise solutions.
We’re proud to be partnering with Ecologi. More than simply tree planting, we invest in projects to help offset the impact of our commercial activities.
Some of the brands we are proud to partner with










Our solutions
Marketing Campaigns
Nothing builds an emotional bond with your brand like a branded gift sent to a customer, supplier, work colleague or prospective partner. We can design, source and fulfil, managing the whole process from start to finish, to support your campaign seamlessly.
Digital Ranges
Whether you need a fully transactional, multi-lingual and multi-currency webstore, a pop-up shop for a specific campaign or event, or an instant merchandise shop with fast turnaround, our team will work with you to create safe, secure and convenient tailored digital retail solution.
Event Support
Events are back and we’re here to help! For internal conferences and team-building days, tradeshows or public events, we have the knowledge, experience and supply chain to deliver what you need, when you need it.
Uniforms
For event clothing or for staff in the workplace, we have the widest range of apparel, all branded and/or personalised in-house, to make your team look professional and united.
Bespoke Kits
Whether for new starters, company celebrations, employee wellness or customer goodwill, we can create tailored kits for every purpose. Our bespoke packs can be designed to meet your budget and campaign goals – and we manage the whole multi-gift solution process in-house, from concept, design and sourcing to picking, packing and shipping.
Retail Ranges
We develop gifts with purchase incentives and rewards for use by retailers to support specific campaigns and to elevate the value of their products.
Reward Programmes
Staff reward incentives are a great way to boost team morale and grow brand affinity – our reward programmes can be tiered or themed to suit your budget and goals.
VIP Gifts
We have a range of discerning gifts designed to impress your corporate VIPs and with exquisite packaging available too, we’re here to make you look great, every step of the way.
And Much More...
Whatever you need, our team of designers and procurement professionals can help. We can create bespoke solutions fast and efficiently to meet your exact requirements. As a one-off project or complete outsourced programmes, we have the flexibility to assist you. Get in touch today and let’s see how we can help.
Accreditions